As cyber attackers continue to take advantage of vulnerable people, processes, and technology, they are now expanding their operations beyond “traditional” targets. It seems that nothing is outside of their jurisdiction and no one is 100 percent safe from their malicious campaigns. Although organizations are making strides in the right direction to protect themselves, as soon as one attack vector is thwarted, another quickly becomes exposed.
Today’s adversaries are now focusing their efforts on APIs in particular, which are quickly becoming the new attack frontier. In fact, recent reports suggest that by 2022, API abuses will be the vector most responsible for data breaches within enterprise Web applications. This is primarily due to the extensive growth of API implementations world-wide, providing a new target that hasn’t been widely exploited as of yet. With this, protecting APIs is becoming more important than ever.
While the concepts of API security are somewhat new, the attacks that can be performed through them are not. Most organizations have been experiencing similar threats targeting their networks and internet-facing applications for years. Now, they must focus their efforts on mobile apps, APIs, and back-end servers being targeted by similar methods as seen in the past. Before discussing the risks associated with today’s APIs, we must first understand exactly what makes them unique and vulnerable.
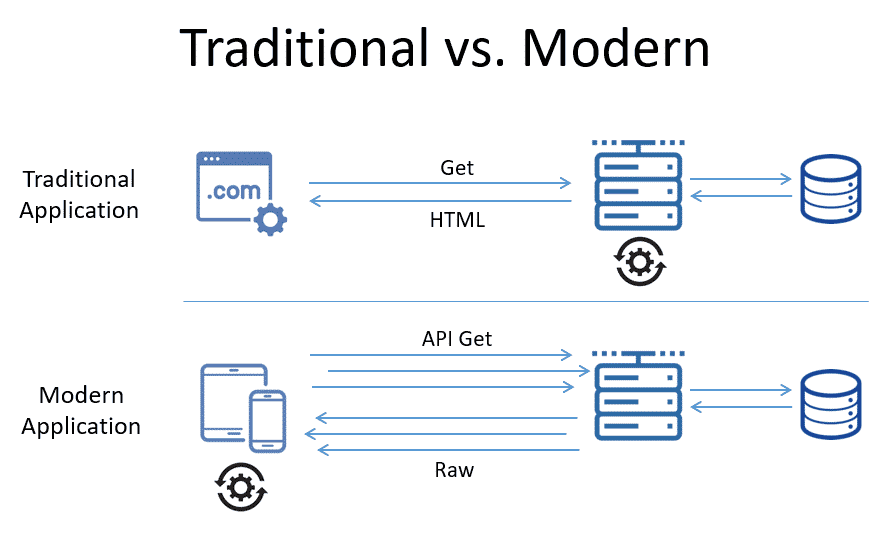 When viewing the graphic, we see that in the modern application at the bottom, the downstream server acts more like a proxy for the data consumed by the API-based app. The rendering component in this instance is the client who consumes the raw data, not the server itself. Let me further explain.
Many can remember the early days of using smartphones and traditional websites when trying to reserve a flight, for example. People would open a browser on their phone and attempt to use an airline website that was designed for a large computer monitor, not a small smartphone screen. This didn’t work too well, and as a consequence, companies began to update their websites by making them more smartphone friendly. Although this improved the client’s experience, it still was quite cumbersome to navigate and complete an airline reservation.
As a result, airlines, hotels, car rental companies, etc. began to develop their own mobile apps. Instead of trying to reserve a flight using a mobile-friendly version of the airline’s website and a browser on their phone, people now download and install the airline’s mobile app and use it exclusively when reserving flights directly from their smartphones. Concerning how this operates in conjunction with APIs, what’s different?
Well, when making a flight reservation using an airline mobile app, the app uses API calls that are interacting with back-end servers primarily to retrieve data about flight schedules, availability, pricing, seats, etc. The app is also interacting with the user, allowing them to specify travel dates, departure and arrival cities, seat selection, and purchase options. In this case, the smartphone is performing almost all of the processing load of the flight reservation within the mobile app itself, without the usage of a browser. Although this has tremendously improved the flight reservation experience overall when using a smartphone, it begs the question: are APIs just as vulnerable to cyberattacks as browser-based applications?
When viewing the graphic, we see that in the modern application at the bottom, the downstream server acts more like a proxy for the data consumed by the API-based app. The rendering component in this instance is the client who consumes the raw data, not the server itself. Let me further explain.
Many can remember the early days of using smartphones and traditional websites when trying to reserve a flight, for example. People would open a browser on their phone and attempt to use an airline website that was designed for a large computer monitor, not a small smartphone screen. This didn’t work too well, and as a consequence, companies began to update their websites by making them more smartphone friendly. Although this improved the client’s experience, it still was quite cumbersome to navigate and complete an airline reservation.
As a result, airlines, hotels, car rental companies, etc. began to develop their own mobile apps. Instead of trying to reserve a flight using a mobile-friendly version of the airline’s website and a browser on their phone, people now download and install the airline’s mobile app and use it exclusively when reserving flights directly from their smartphones. Concerning how this operates in conjunction with APIs, what’s different?
Well, when making a flight reservation using an airline mobile app, the app uses API calls that are interacting with back-end servers primarily to retrieve data about flight schedules, availability, pricing, seats, etc. The app is also interacting with the user, allowing them to specify travel dates, departure and arrival cities, seat selection, and purchase options. In this case, the smartphone is performing almost all of the processing load of the flight reservation within the mobile app itself, without the usage of a browser. Although this has tremendously improved the flight reservation experience overall when using a smartphone, it begs the question: are APIs just as vulnerable to cyberattacks as browser-based applications?
API-Based Apps vs. Traditional Applications
API-based apps are significantly different than traditional applications. In the past, users / visitors would access a webserver via a browser (for example) and most of the “data processing” was performed on the server itself. As client devices became more varied, and increasingly powerful with faster CPUs, extensive memory, more bandwidth etc., much of the logic moved away from being performed on back-end servers to the front-end (i.e. on the client device itself) as highlighted in the graphic below.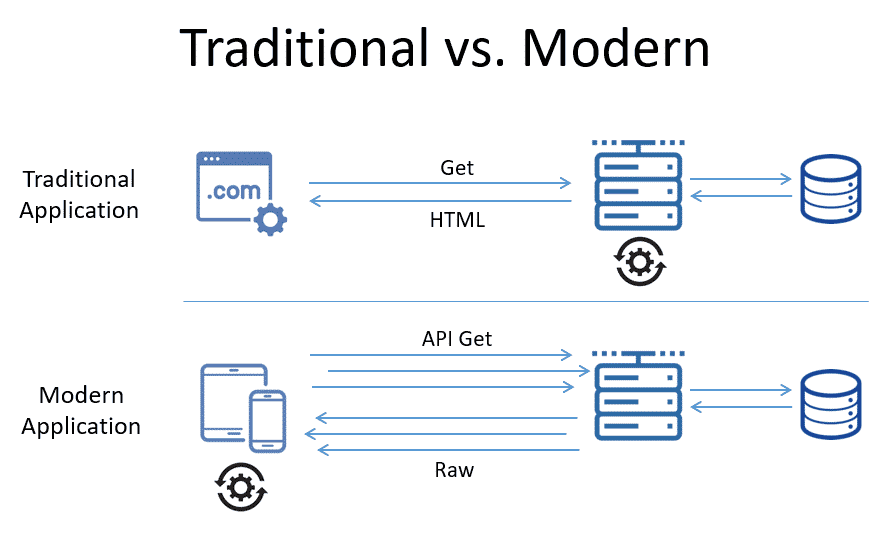 When viewing the graphic, we see that in the modern application at the bottom, the downstream server acts more like a proxy for the data consumed by the API-based app. The rendering component in this instance is the client who consumes the raw data, not the server itself. Let me further explain.
Many can remember the early days of using smartphones and traditional websites when trying to reserve a flight, for example. People would open a browser on their phone and attempt to use an airline website that was designed for a large computer monitor, not a small smartphone screen. This didn’t work too well, and as a consequence, companies began to update their websites by making them more smartphone friendly. Although this improved the client’s experience, it still was quite cumbersome to navigate and complete an airline reservation.
As a result, airlines, hotels, car rental companies, etc. began to develop their own mobile apps. Instead of trying to reserve a flight using a mobile-friendly version of the airline’s website and a browser on their phone, people now download and install the airline’s mobile app and use it exclusively when reserving flights directly from their smartphones. Concerning how this operates in conjunction with APIs, what’s different?
Well, when making a flight reservation using an airline mobile app, the app uses API calls that are interacting with back-end servers primarily to retrieve data about flight schedules, availability, pricing, seats, etc. The app is also interacting with the user, allowing them to specify travel dates, departure and arrival cities, seat selection, and purchase options. In this case, the smartphone is performing almost all of the processing load of the flight reservation within the mobile app itself, without the usage of a browser. Although this has tremendously improved the flight reservation experience overall when using a smartphone, it begs the question: are APIs just as vulnerable to cyberattacks as browser-based applications?
When viewing the graphic, we see that in the modern application at the bottom, the downstream server acts more like a proxy for the data consumed by the API-based app. The rendering component in this instance is the client who consumes the raw data, not the server itself. Let me further explain.
Many can remember the early days of using smartphones and traditional websites when trying to reserve a flight, for example. People would open a browser on their phone and attempt to use an airline website that was designed for a large computer monitor, not a small smartphone screen. This didn’t work too well, and as a consequence, companies began to update their websites by making them more smartphone friendly. Although this improved the client’s experience, it still was quite cumbersome to navigate and complete an airline reservation.
As a result, airlines, hotels, car rental companies, etc. began to develop their own mobile apps. Instead of trying to reserve a flight using a mobile-friendly version of the airline’s website and a browser on their phone, people now download and install the airline’s mobile app and use it exclusively when reserving flights directly from their smartphones. Concerning how this operates in conjunction with APIs, what’s different?
Well, when making a flight reservation using an airline mobile app, the app uses API calls that are interacting with back-end servers primarily to retrieve data about flight schedules, availability, pricing, seats, etc. The app is also interacting with the user, allowing them to specify travel dates, departure and arrival cities, seat selection, and purchase options. In this case, the smartphone is performing almost all of the processing load of the flight reservation within the mobile app itself, without the usage of a browser. Although this has tremendously improved the flight reservation experience overall when using a smartphone, it begs the question: are APIs just as vulnerable to cyberattacks as browser-based applications?
The Risks Associated with APIs
Unfortunately, APIs are also exposed to attacks and at a very high level, API security issues do exist similar to their browser-based counterparts. However, since APIs expose the underlying implementation of a mobile app, and the user’s state is usually maintained and monitored by the client app, plus more parameters are sent in each HTTP request (object IDs, filters, etc.), some of the security issues surrounding APIs are rather unique. For the most part, these issues lead to vulnerabilities that can be categorized into three unique areas of concern:- Exposing sensitive data
- Intercepted communications
- Launching denial of service (DoS) attacks against back-end servers