Summary
The best approach to protecting against SQL injection attacks — which happen when threat actors feed malicious code into SQL databases — is to implement multiple layers of defense, such as validating input received by applications, scanning source code to detect SQL injection vulnerabilities and testing live applications to check how they respond to malicious SQL queries.
SQL injection attacks are the main source of critical vulnerabilities for web applications in 2024, making up 23.4% of all vulnerabilities. To understand this risk better, this article answers the question, ‘what is SQL injection?’, explains SQLi, (meaning SQL injection attacks) and how they impact your organization. It describes how you can protect yourself against this growing and complex threat with the support of application security testing that includes SAST as a core feature.
Let’s start with an SQL injection definition, for those who haven’t heard the term before. SQL commands are a normal part of interacting with databases, allowing applications to read and write data using the language SQL, which stands for Structured Query Language.
However, when threat actors use SQL to insert malicious commands instead of legitimate ones, this is a SQL injection attack, also known as SQLi. By using malicious SQL code, back end databases can be manipulated to access sensitive information, allowing attackers to monitor, extract, delete or share data which they should not have been able to reach.
Common consequences of a SQLi attack include:
- Modifying of database schemas, such as stored functions or processes
- Altering passwords or permissions
- Subverting application logic to change a query
- Modifying of T-SQL statements, leading to more data access
- Testing for database configuration, including storage or server infrastructure
- Launching ransomware or DDoS attacks from inside the database
- Deleting, stealing, or encrypting sensitive or critical data
- Gaining a foothold for long-term monitoring or stealth attacks
- Executing admin operations, including shutdown of the database
Understanding SQLi Attacks by Examples
There are three main methods of injecting malicious input using SQLi.
In-band injection
With in-band injection, the attacker utilizes the same communication channel to inject the code, and view the results. Examples include Error-based SQLi and Union-based SQLi. Error-based SQLi uses database error messages that have not been disabled or logged with restricted access permissions. With these messages an attacker can gain information about the database. Union-based SQLi is also an in-band injection technique, and it uses the UNION SQL operator, taking advantage of multiple SELECT statements which are then returned as part of the HTTP response.
Out-of-band injection
Unlike in-band injection, with out-of-band injection, the attacker injects the code into the application and then relies on special database features to gain access to the sensitive information. These techniques are less common, because they are only used when a threat actor cannot use the same channel to both launch an attack and collect results. One example of an out-of-band injection technique is Microsoft SQL Server’s xp_dirtree command. This can be leveraged to make a DNS request to a malicious server which is under the control of a threat actor.
Blind injection
Finally, the third category is blind injection. These are different in the kind of code that is injected to the database. Instead of manipulating the database to access sensitive information, these commands evaluate how the database is configured, giving the attacker greater information about how they can launch an attack. This is also known as inferential SQLi. The attacker usually sends SQL queries to the database, and then observes the response. By monitoring how long a database waits before responding, or whether the HTTP response changes or remains the same, attackers can infer a TRUE or FALSE outcome, even without data being returned.
How Do Attackers Take Advantage of SQLi Vulnerabilities?
So, why do SQL attacks happen? No development team is intentionally leaving the door open for SQL injections, but there are a number of factors that contribute to the growing problem, and some can be solved by shoring up poor security hygiene.
First, input validation is really critical. Many applications automatically pass commands to the database with no validation, and if an attacker has inserted malicious SQL commands – there would be no way of knowing. It’s also important to check legacy code, as many applications have sat dormant for years, and what was secure when it was written may not be sufficient today. Code which is no longer necessary should be removed, as its only purpose is to add risk to your environment. This level of due diligence is not only about code. Other ways that attackers launch SQLi attacks are via unpatched applications and legacy software.
A lack of testing is also part of the growing risk of SQLi. You can often detect SQL vulnerabilities with common tests such as looking for the single quote character ‘, analyzing differences in application responses with SQL-specific syntax, or inputting payloads in SQL queries designed to trigger time delays and measuring the time taken to respond. Common locations for SQLi vulnerabilities are in the WHERE clause of a SELECT query, in UPDATE statements, or in the table or column name of SELECT statements. Unfortunately, this is by no means a comprehensive list, and vulnerabilities can occur anywhere – making manual testing an insufficient answer to the SQLi problem.
How to Detect and Prevent SQLi
While there are some simple ways to encourage developers to reduce the likelihood of SQL injection attacks, such as deleting error messages and restricting the maximum length of data input, to be truly secure against this threat – Application Security Testing (AST) is paramount. These automated tools shift security early in the software development lifecycle, and actively search for where applications connect to a database and test its vulnerabilities. Robust AST will include:
Input validation: A thorough validation of all application input, with a broad range of attack scenarios including known threats and edge cases.
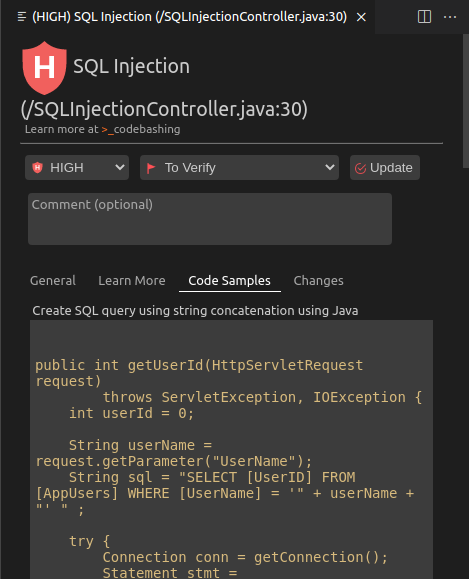
Static Application Security Testing: SAST scans the source code before deployment, detecting vulnerabilities at the code level, ahead of time.
Dynamic Application Security Testing: DAST finds the vulnerabilities in live applications, knowing security can evolve past deployment.
Simulations: Testing applications for SQL vulnerabilities by attempting to insert malicious commands, and evaluating the response.
Protect from SQL Injection Attacks Today!
Get everything your enterprise needs to integrate AppSec across every stage of the SDLC and secure your applications from code to cloud on a unified application security platformrnrn
Using Checkmarx to Prevent SQL Injection Attacks
Checkmarx One is our leading application security testing solution, and it is a powerful tool to prevent SQL injection attacks in your applications, . identifying potential SQL injections for developers to fix, ahead of deployment. It includes a comprehensive next-generation SAST tool that scans against application security risks at the earliest stage, allowing you to shift left, while the whole platform supports shifting everywhere – from code to cloud..
Integrated with the IDE, build management tools, bug tracking and source repositories, developers can work without friction – continuing their workflow as they prefer, and fixing source code issues with ease. In the background, thorough and customizable scans and testing give you peace of mind that all code is going to production without vulnerabilities. If a problem or risk is found, the fix is explained in natural language, alongside the exact code snippet to make the change.
Looking to prevent the risk of SQL attacks in your environment? Learn more about Checkmarx by requesting a demo.
